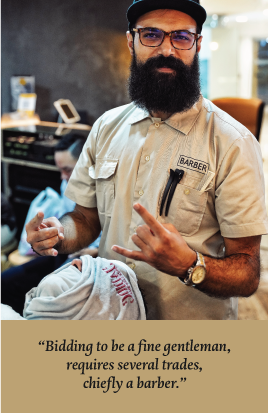
ABOUT US
HUUK BARBERSHOP
Les Meilleurs Casinos en Ligne avec Bonus Sans Dépôt en Belgique
Dans le monde passionnant des casinos en ligne, les joueurs belges sont constamment à la recherche de la meilleure offre pour maximiser leur expérience de jeu. Parmi les préférences populaires, les bonus sans dépôt représentent une option attrayante pour les nouveaux utilisateurs et les joueurs expérimentés. Ces bonus permettent de découvrir de nouvelles plateformes sans risquer ses propres fonds. Les casinos en ligne veulent attirer de nouveaux joueurs et les garder engagés, ce qui rend ces bonus particulièrement populaires en Belgique.
En Belgique, plusieurs casinos en ligne se démarquent grâce à leurs offres généreuses et leurs services de qualité. Ils se battent pour attirer de nouveaux joueurs en offrant des casino bonus sans depot belgique, permettant ainsi aux utilisateurs d’explorer les jeux et de tester leurs chances sans investir de capital initial.
| Fonctionnalité | Description |
|---|---|
| Bonus d’inscription | Offre sans dépôt pour tester la plateforme. |
| Jeux disponibles | Large sélection incluant les machines à sous, le poker, et plus. |
Avec l’évolution de la technologie, les casinos en ligne belges ont optimisé leurs plateformes pour être accessibles sur les appareils mobiles. Que ce soit par un site web mobile ou une application dédiée, les joueurs peuvent accéder à leurs jeux préférés où qu’ils soient et à tout moment, assurant une expérience fluide et immersive.
La sécurité et le soutien sont des aspects cruciaux pour les joueurs en ligne. Les casinos en Belgique investissent dans des technologies de pointe pour assurer la protection des données personnelles et des transactions financières. De plus, un service client disponible 24/7 garantit une assistance constante pour répondre à toutes les questions ou préoccupations des joueurs.
- Bonus de fidélité pour les joueurs réguliers.
- Programme VIP avec des récompenses exclusives.
- Options de retrait rapide et sécurisé.
- Jeux en direct avec croupiers réels.
- Compatibilité avec divers appareils et systèmes d’exploitation.
En conclusion, les casinos en ligne avec des bonus sans dépôt en Belgique offrent une opportunité précieuse d’explorer le monde du jeu avec un risque minimal. Les offres variées et les services de qualité garantissent une expérience de jeu enrichissante et sécurisée pour tous les types de joueurs. Ces plateformes continuent d’évoluer, attirant de plus en plus de passionnés de casinos à travers le pays.
At huuk barbershop, we are dedicated to providing affordably priced, unparalleled hair styling and grooming services that are tailored to every client and their lifestyle in a distinctively unique atmosphere. As customers are our number one priority, we value every client and their individual needs.
Welcome to Huuk Barbershop, your premier destination for world-class grooming. We have mastered the art of blending traditional techniques with modern trends, uniquely reflecting the fusion offered by Casino Kingdom. Here, as in the dynamic world of high-stakes online casinos, we believe in providing exquisite services.
Our experienced barbers take a meticulous approach to their work, satisfying the diverse styling needs of our customers. Just as Casino Kingdom https://icasinoreviews.co.nz/casino-kingdom/ is renowned for its wide selection of games, Huuk Barbershop boasts a wide range of grooming services. We strive to provide services that not only meet our customers’ requirements but exceed their expectations.
The essence of responsible gambling at Casino Kingdom reflects our commitment to providing grooming services that meet individual needs, ensuring that every haircut, trim, and shave is performed with precision. We invite you to enjoy the royal atmosphere at Huuk Barbershop, which mirrors the exciting experience offered by online casinos.